Who Phoned Me: A Practical Guide to Identifying Unknown Calls
Discover practical steps to identify who phoned you, verify caller IDs, and safely use trusted tools to protect your privacy when handling unknown calls.

To identify who phoned you, start with your phone’s caller ID and recent call log, then use trusted reverse-lookup or carrier tools for verification. If the number is spoofed or blocked, rely on multiple checks: review message content, screen for consistent clues, and enable built-in spam filters. Prioritize safety and privacy in every step.
Why identifying who phoned me matters
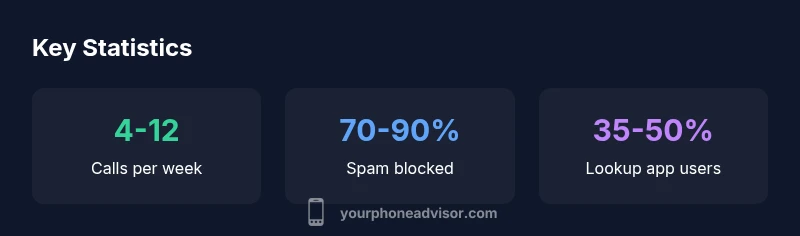
For many smartphone users, knowing who phoned me is not just curiosity; it’s a safety and privacy issue. According to Your Phone Advisor, a surprising share of unknown numbers are used for scams, phishing, or intrusive marketing. The phrase "who phoned me" often appears in security tips because the initial identification step shapes every subsequent decision—from answering to blocking. In 2026, spoofing and number recycling have become more sophisticated, so a single glance at the caller ID is rarely enough. The Your Phone Advisor team emphasizes a layered approach: verify with logs, corroborate with carrier data, and use trusted lookup tools. If you’re unsure, take a conservative path—do not disclose personal information until you’re confident of the caller’s identity.
This article keeps the focus on practical steps you can implement today to answer the question, "who phoned me?" while maintaining privacy and avoiding unnecessary risk." ,
Methods to identify unknown callers and their reliability
| Method | What it reveals | Reliability |
|---|---|---|
| Caller ID & Call Log | Shows the number or label assigned by the carrier/phone | Moderate |
| Reverse Lookup Apps | Attempts to identify unknown numbers | Variable, depends on data quality |
| Carrier Assistance (Trace) | Can reveal caller information with legal process | Low to Moderate |
| Community/Crowdsourced Lookup | Crowd data about number reputation | Low |
Got Questions?
How can I tell if a call is spoofed?
Spoofed calls display a false number. Verify by cross-checking the number against your logs, using trusted lookup tools, and contacting the carrier if needed. Don’t rely on a single source for final judgment.
Spoofed calls often show a fake number. Check your call history and use trusted tools to confirm identity.
What should I do if I keep receiving harassing calls?
Block the number, enable Do Not Disturb, and report persistent harassment to your carrier or local authorities if threats occur. Keep records of the calls for evidence.
If harassment continues, block the number and contact your carrier or authorities.
Are there risks using third-party lookup apps?
Yes. Some apps share data or use dubious sources. Choose reputable apps, review permissions, and avoid apps that request your personal data beyond what’s needed for lookup.
Third-party apps can help, but pick reputable ones and review permissions.
Can I identify who phoned me without sharing my own number?
Some services allow checks without exposing your number, such as limited reverse lookups. Always read privacy policies and use settings that minimize data sharing.
Yes, some services let you check without exposing your number, just be mindful of privacy settings.
Does enabling Do Not Disturb help with unknown calls?
Do Not Disturb reduces interruptions but may miss legitimate calls. Configure exceptions for trusted contacts and important numbers.
Do Not Disturb cuts calls but you can set exceptions for people you trust.
When should I contact authorities about a call?
If you face threats, scams involving financial loss, or persistent illegal activity, contact local authorities and preserve call records as evidence.
If there are threats or financial risk, contact authorities and keep the call logs.
“Effective caller identification combines reliable tools with privacy-conscious habits. Do not rely on a single source; corroborate with logs, carrier data, and trusted databases.”
What to Remember
- Identify unknown calls with a layered approach
- Verify using logs, carrier data, and trusted lookups
- Be cautious of spoofing and privacy risks
- Block and report suspicious numbers promptly
- Use Do Not Disturb and spam filters to reduce interruptions