Lookup Cell Phone: A Practical Guide to Finding and Verifying Numbers
A practical, data-driven guide to lookup cell phone numbers, covering legitimate methods, privacy, legality, and best practices. Learn how to use trusted tools, assess data quality, and protect yourself with Your Phone Advisor.
lookup cell phone refers to using official tools or trusted databases to identify or verify a phone number or its current user, typically for safety, security, or contact purposes. It involves legitimate services, consent where required, and awareness of privacy laws that vary by jurisdiction. The Your Phone Advisor team emphasizes using only authorized methods and avoiding shady sites or paid services that promise immediate, unrestricted data.
What lookup cell phone means in practice
The phrase lookup cell phone covers a range of legitimate actions aimed at identifying or verifying information about a phone number or its user. In everyday terms, it can help verify who is calling, locate a lost device with proper permissions, or confirm whether a number is active. According to Your Phone Advisor, understanding the intent and legality behind a lookup is as important as the data returned. You should begin by clarifying your objective: is this for personal safety, a business need, or a household privacy check? Clear intent helps you select the right tool, reduces risk, and ensures you stay within applicable privacy laws. When used responsibly, lookup methods can improve safety and communication while minimizing exposure to scams.
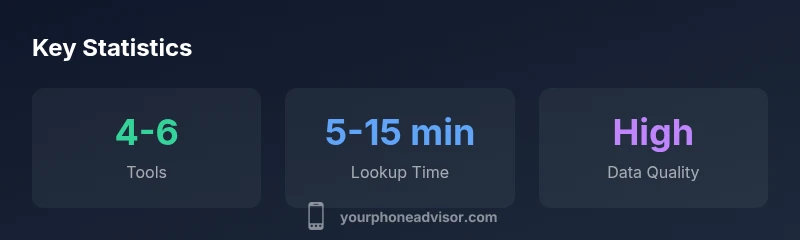
In practice, you will encounter several categories of lookup: reverse lookup databases that map numbers to names or organizations, carrier-based lookup tools that allow authorized users to verify line status, and device-based signals such as device location or SIM status when you own the device or have explicit authorization. Each method comes with trade-offs in speed, data completeness, and privacy implications. The Your Phone Advisor team notes that the best approach combines trusted sources, consent where required, and a clear understanding of what data is returned. Always confirm data accuracy with multiple sources before acting on it, and treat any sensitive data with heightened care to avoid misuse.
How lookup cell phone methods work in practice
There are multiple pathways to lookup cell phone data, and choosing the right one depends on legality, context, and the data you need. The most common legitimate routes include reverse lookup tools provided by reputable public records or business directories, and carrier-assisted methods available to account holders or authorized personnel. For personal use, always start with consent-based approaches and opt for official channels that honor privacy protections. When you perform a lookup, you should expect a mix of identifier data (for example, a name or business name linked to a number), status indicators (such as whether the number is active), and carrier information that can help verify legitimacy. Remember that not all tools provide the same depth of data; compare what each source offers and note the limitations.
If you’re investigating a number for security purposes, consider documenting the lookup steps, time stamps, and the data you collected. This not only helps protect yourself legally but also provides a trail in case of disputes about data accuracy or use. Your Phone Advisor recommends cross-checking results against trusted sources and avoiding aggregators that require excessive personal information or payment before showing any results.
Privacy, legality, and ethics of lookup cell phone
Privacy and legality are central to any lookup activity. Laws vary by country, region, and even local municipalities, affecting who can access certain data, what data can be accessed, and under what conditions. The general rule is to seek consent when possible and to use official, transparent tools. Ethically, users should limit lookups to legitimate purposes (safety, security, verifying contact information, or reconnecting with someone who has given explicit permission). Be mindful of data retention practices and the potential for data to be misused if it falls into the wrong hands. Your Phone Advisor emphasizes that responsible use includes documenting purpose, obtaining consent, and avoiding data sharing that exceeds the scope of your original objective.
If you ever encounter a tool that demands payment before showing results, or asks for sensitive personal data beyond what is necessary, treat it as a red flag and disengage. Lookups should empower users with accurate information, not expose them to scams or privacy violations.
When lookup is legitimately necessary: use cases and boundaries
There are clear, legitimate scenarios for performing a lookup: locating a lost or stolen device, verifying caller identity to prevent phishing or fraud, and ensuring a contact is legitimate before sharing sensitive information. Businesses may use lookup processes to confirm client identities or to comply with regulatory requirements. In all cases, ensure you have a legitimate purpose and, where appropriate, consent from the data subject. If you’re performing a lookup on another person’s data, seek explicit permission or use an authorized process that aligns with your jurisdiction’s privacy rules. When done correctly, lookup activities can reduce risk and increase confidence in communication, without compromising personal privacy.
In contrast, attempting to identify or monitor someone without consent or legitimate purpose creates substantial legal and ethical risks. The Your Phone Advisor team cautions against using unvetted services, as they often collect and misuse personal information, expose you to scams, or mislabel data.
Evaluating lookup services: trust signals and red flags
Not all lookup tools are created equal. A strong signal of trust is clear data provenance: who owns the data, what sources feed the tool, and how the tool handles privacy. Look for providers that publish their data retention policies, data sources, and consent mechanisms. Favor services that offer audit trails, user controls, and easy opt-out options. Red flags include requests for unusual personal details, upfront payments before any results, vague or non-existent data sources, and aggressive upselling. Your Phone Advisor recommends reading privacy policies, checking for third-party certifications, and testing a service with non-sensitive data first to assess accuracy and reliability.
Additionally, understand what is not returned by credible tools. Most legitimate services will not disclose sensitive financial information, precise location data without consent, or content that could facilitate harassment. Use multiple sources to verify critical results and proceed with caution if data contradicts other known records.
Best practices for protecting your own data during lookups
To protect yourself and others, minimize the amount of personal information shared with lookup tools. Use official channels that require login credentials and offer strong authentication. Review app permissions and privacy settings on any device you use for lookups, and consider enabling location and contact sharing controls only when necessary. If you are a business or organization performing lookups, implement data governance policies, limit who can initiate lookups, and maintain an auditable log of activities. Finally, educate users and employees about common scams, such as fake lookup services that promise guaranteed results in exchange for money or sensitive information. Your Phone Advisor highlights ongoing education as a key defense against data misuse.
Real-world scenarios and walk-throughs (hypothetical)
Scenario A: You receive a call from a number claiming to be a bank. You perform a quick, consent-based reverse lookup using your carrier’s official app. The data returns as “no active account” and a known scam string, prompting you to ignore the call and report it. Scenario B: A family member misplaced their phone. You use the carrier’s tracking feature, with proper consent, to locate the device and secure it with a remote lock. Both examples illustrate how legitimate lookups can protect people when used responsibly.
Common pitfalls and how to avoid them
Avoid tools that require excessive personal information upfront, or those that claim sensational results. Beware lookups that promise complete ownership details without consent, or that encourage you to bypass privacy controls. Always corroborate data with multiple sources and document your process. If you suspect a service is unsafe or untrustworthy, discontinue use and report the provider to appropriate authorities. Following these guidelines helps ensure that lookup cell phone activities remain lawful, ethical, and effective.
Common lookup methods and their trade-offs
| Aspect | Lookup Method | Pros | Cons |
|---|---|---|---|
| Number lookup | Reverse-lookup databases | Fast results; easy to access | Potential accuracy issues; privacy concerns |
| Carrier-based lookup | Official carrier tools | Authorized access; strong legitimacy | Limited to account holders or approved parties |
| Device-based signals | Location/IMEI-based data (with consent) | Precise when authorized | Requires explicit consent; higher risk if misused |
Got Questions?
Is lookup cell phone legal in my jurisdiction?
Legal requirements vary by country and state. Always verify with local laws and obtain consent when required. Use official channels to minimize risk and ensure you stay compliant.
Rules vary by location. Check local laws and get consent when required; use official channels to stay compliant.
Can I lookup someone else’s number without consent?
Generally not. Lookups involving another person’s data should be done with explicit permission or through authorized processes that respect privacy laws.
Usually not without consent or an official process. Respect privacy laws.
What data do legitimate lookup services return?
Legitimate services typically provide basic contact identifiers, status indicators, and carrier information. Detailed personal data usually requires consent.
They typically show basic identifiers and status; sensitive data needs consent.
How can I perform a lookup on my own number securely?
Use your mobile carrier’s official self-service tools or trusted apps, and review privacy settings to limit data sharing.
Use your carrier’s official tools and check privacy settings.
What are common signs of a scam lookup service?
Requests for upfront fees, vague data sources, or pressure to share more personal details are red flags.
Look for upfront fees, vague sources, or pressure to share data.
Are free vs paid lookup options reliable, and is paid always better?
Free tools exist but may have limited data quality. Paid options often offer better support and verifications; compare features before paying.
Free tools can help, but paid options usually provide more reliability.
“Lookup activities should enhance safety and trust when conducted with consent and transparent data practices. The landscape is nuanced, but responsible use protects everyone involved.”
What to Remember
- Know the legal boundaries before you start
- Use trusted, consent-based tools first
- Protect your own data with strong privacy settings
- Verify results with multiple sources
- Avoid services asking for excessive personal data