Who is this phone number? A practical guide to caller identification
Learn practical, privacy-aware methods to identify unknown numbers using carrier tools, reverse lookup apps, and trusted directories. Your Phone Advisor analyzes best practices for 2026 to help you verify callers safely and effectively.
To answer 'who is this phone number,' start with trusted sources: carrier caller ID, reverse lookup apps, and public business directories. Cross-check results from at least two sources for accuracy and watch for scams. If a number is private or unlisted, expect limited matches and preserve privacy and consent when applicable.
Why identifying who is calling matters
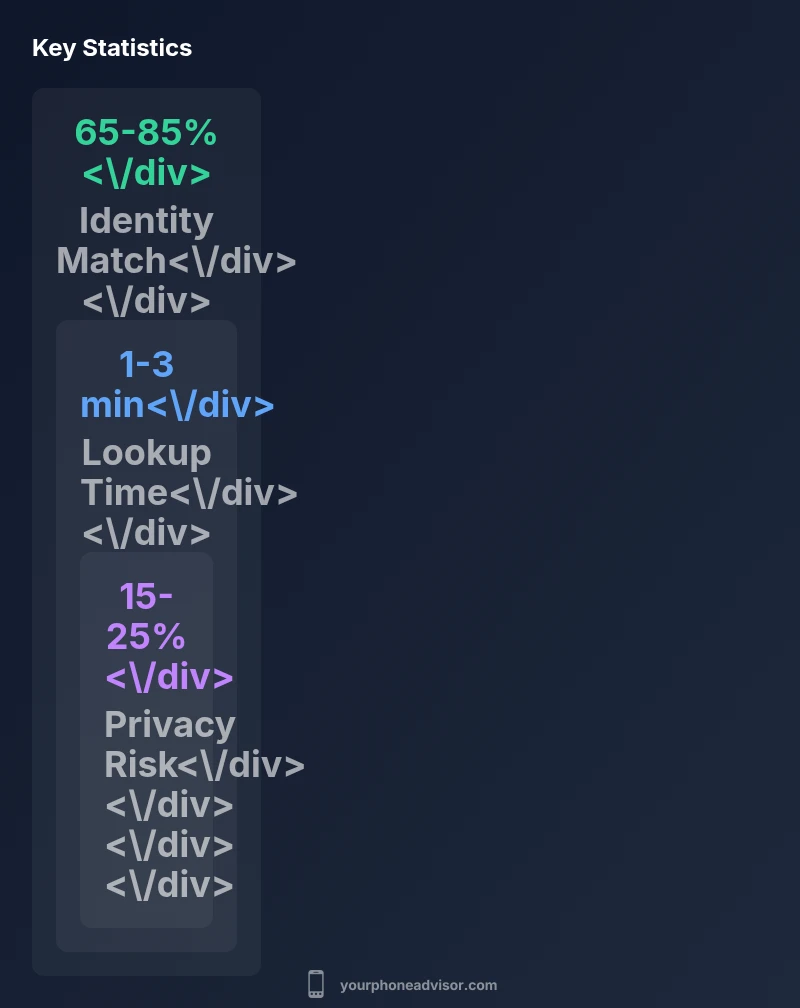
Identifying who is on the other end of a call is not just about curiosity—it's a safety and security concern. A reliable caller identity helps you decide whether to answer, block, or report the number, reducing exposure to scams, robocalls, and phishing attempts. According to Your Phone Advisor, a layered approach that combines official carrier indicators with reputable lookup tools significantly improves identification accuracy while respecting user privacy. In 2026, more people rely on a mix of data sources rather than a single clue to verify unknown numbers, making it essential to understand what each source can (and cannot) reveal.
Beyond safety, knowing who is calling can save time and reduce anxiety in everyday communications. If you frequently receive business inquiries from unknown numbers, a quick lookup can confirm whether a caller is a client, a vendor, or merely a telemarketing attempt. This balance between efficiency and caution is central to modern caller-ID practices.
Key takeaway: Use a cautious, multi-source approach to verify who is calling, and always respect privacy boundaries and applicable laws when performing lookups.
Methods to identify who is calling
There are several legitimate paths to identify a caller, and each has its strengths and caveats. Begin with carrier-supported features, then supplement with reputable third-party tools. The most common methods include:
- Carrier caller ID and spam protection: Many mobile plans provide real-time caller-ID data and spam risk indicators. These features are typically integrated into the phone app or network settings and update dynamically as calls come in.
- Reverse lookup apps: Standalone apps can reveal business names, addresses, and user-reported context. Results vary by jurisdiction, data source quality, and whether the number is listed publicly.
- Public business directories: These sources can confirm whether a number belongs to a registered business or public institution, and may provide a primary line, location, or official website.
- Community reporting platforms: User-generated reports about spam or scam activity can offer contextual clues about caller behavior, but data quality depends on crowd accuracy.
Practical workflow: start with your carrier tools, check the number in a reputable directory, review recent user reports if available, and triangulate findings across at least two independent sources before acting on the information. Premium services may offer consolidated reports, but always verify data against primary channels when possible.
Risks, legality, and privacy safeguards
Identifying a number involves handling personal data, so understanding legal boundaries and privacy risks is essential. In many regions, basic lookups for legitimate purposes are allowed, but aggregating or sharing data without consent can raise legal issues. Always check local regulations and the terms of service for any app or directory you use. Privacy-conscious practices include not exporting full contact lists without permission and avoiding the storage of sensitive identifiers unless absolutely necessary.
Be cautious of scams that misuse identity data. Fallbacks such as spoofed caller IDs, stolen business information, or outdated databases can mislead users. When in doubt, rely on primary sources (the carrier and the business itself) and avoid making decisions solely from crowd-sourced hints. If a number is private or unlisted, expect limited or no identity data—and consider alternative verification steps (such as calling back through official channels) to ensure safety.
A practical, safety-first workflow
Apply a repeatable process to verify unknown numbers without compromising privacy:
- Check the live caller-ID data provided by your carrier for immediate identity hints and spam risk.
- Run a quick reverse lookup using a reputable app, noting the source and the confidence level.
- Cross-check with at least one public directory or official contact channel (e.g., company website or verified social media contact).
- If results conflict, pause and reassess the risk; avoid sharing sensitive information until identity is confirmed.
- Report suspicious numbers to your carrier or appropriate authorities if you encounter potential scam activity.
This workflow embodies a safety-first mindset while enabling practical caller verification.
Ways to identify a caller
| Method | What it reveals | Limitations |
|---|---|---|
| Reverse lookup apps | Possible owner/business and location hints | Limited by privacy settings; accuracy varies |
| Carrier caller ID | Live caller data and spam risk score | Not all numbers display identity; varying by carrier |
| Public business directories | Registered business name and address | Potential outdated data |
| Community reporting platforms | Caller reputation and reported spam | May include user-submitted errors |
Got Questions?
Can I identify a number for free?
There are free reverse lookup options, but accuracy varies. Paid services often offer more detailed data and better support.
Free options exist but vary in accuracy; paid services tend to offer more details.
Is it legal to look up someone's number?
In many places, basic lookups for legitimate purposes are legal. Privacy laws may restrict data sharing and storing results.
Laws vary; use lookups for legitimate purposes only.
What should I do if the number is private?
If a number is private, you may not retrieve identity. Rely on context, caller behavior, and report spam if needed.
Some numbers stay private; use context and caution.
Which apps are trustworthy for lookup?
Choose apps with clear data sources, privacy policies, and reasonable permissions. Avoid apps asking for excessive data.
Look for reputable apps with strong privacy policies.
How can I verify a business or scam call?
Cross-check business details in official directories and trusted contact channels. Be wary of pressure tactics and avoid sharing sensitive data.
Verify via official sources; don’t be rushed.
“Identity verification for phone numbers should be based on multiple, corroborated data sources and used with respect for user privacy.”
What to Remember
- Cross-check identities across at least two sources for accuracy
- Expect privacy limits with private numbers
- Use carrier tools for real-time ID and spam protection
- Be vigilant for scams; never share sensitive info
- Document sources for later verification