What to Do If Your Phone Is Hacked
Learn practical, step-by-step actions to secure a hacked phone, protect accounts, and prevent future breaches. This guide from Your Phone Advisor walks you through immediate steps, data backup, and long-term security habits.

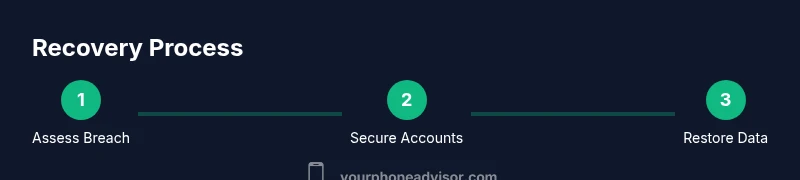
If your phone is hacked, act quickly: secure accounts, change passwords, enable two-factor authentication, and run a malware scan. For the query what to do phone hacked, disconnect from Wi‑Fi, avoid reusing passwords, review app permissions, and back up data. If the breach persists, update the OS, reset the device to factory settings, and contact your carrier for assistance.
Immediate First Steps
If you suspect your phone has been compromised, begin with rapid containment. Turn off or disconnect from the internet if you can do so safely, and avoid using the device for sensitive tasks like banking or password managers until you regain control. If you're not sure what to do phone hacked, this section starts with the essential, time-sensitive actions to minimize damage and buy you time to assess the breach. In many cases, the goal is to stop any ongoing remote access, preserve evidence for later review, and prevent further data loss. Stay calm, document what you notice, and proceed to the next steps with a clear plan. According to Your Phone Advisor, acting quickly is one of the most effective ways to limit the impact of a mobile breach. This opening section sets the stage for stronger safeguards and a safer recovery path, without assuming you are an expert. The steps that follow are designed to be actionable for everyday users, not IT professionals, and they prioritize your safety and privacy above all.
Secure Your Accounts and Personal Data
Breached devices often expose login credentials and personal information. Begin by logging into trusted devices (not the compromised phone) and changing passwords for critical accounts: email, banking, social media, and cloud storage. Enable two-factor authentication (2FA) wherever possible, using an authenticator app rather than SMS when available. Review recovery options and security questions to ensure they aren’t easily guessed. Check recent login activity and revoke sessions on unfamiliar devices. If you’re unable to access some accounts from the compromised device, do this from a trusted computer or another phone. Finally, audit recent app activity for anything unexpected and remove suspicious programs.
Identify and Remove Malicious Apps
Malicious software often masquerades as legitimate utilities. Go through installed apps and remove anything you don’t recognize or that requests unusual permissions. Pay attention to apps with excessive permissions (SMS, contacts, mic, camera) or those recently installed shortly before unusual device behavior. After uninstalling, reboot the device and run a reputable mobile security scan from a trusted source. If you cannot uninstall an app, disable its permissions and restrict its background activity. Document any suspicious apps you remove for reference during follow-up reviews.
Stop Data Exfiltration: Network and Permissions
Some hacks rely on covert data transmission. Disable or restrict background data for apps that don’t need constant connectivity, and review network settings to remove unfamiliar VPNs or proxy configurations. Turn off developer options or unknown USB debugging in the privacy settings if you don’t know their source. Revoke unnecessary permissions for all installed apps, especially access to contacts, location, microphone, and SMS. Consider enabling a firewall/monitoring tool where available and ensure your device is not enrolled in any staging or beta program that you did not authorize.
Protect Your Communications: Phone, Messaging, and Email
A compromised phone can intercept messages and calls. Review every messaging app for security warnings and ensure chats are end-to-end encrypted where possible. Change passwords and enable 2FA on messaging and email apps you use, particularly those tied to banking or social accounts. If you use messaging on multiple devices, re-authenticate each one and log out devices you don’t recognize. If you suspect messages were altered or filtered (phishing or spoofed alerts), report them to the provider and avoid clicking links from suspicious messages.
OS Updates, Backups, and Factory Reset Considerations
Keeping the operating system and apps current is crucial for patching known vulnerabilities. Install the latest OS update and all recommended security patches, then update your essential apps from official sources. Create a clean backup of your data to a trusted location before making major changes. If the device remains compromised after standard cleanup, a factory reset from the device’s settings can restore a clean state, provided you have a verified backup and have reinstalled only trusted apps from official stores. After reset, restore data selectively and reconfigure security settings.
What to Do If You Can’t Access Your Accounts
If a hacked device prevents you from logging into critical accounts, use alternate recovery methods from a trusted device. Contact each service’s support channels and explain that you believe your account was compromised. Prepare to provide recovery details and verify your identity. If you suspect SIM swap or carrier-level fraud, contact your mobile carrier immediately to resecure the line and request a SIM lock or temporary suspension of new SIM activations. In parallel, notify financial institutions if banking credentials were affected and monitor statements for unauthorized activity.
Involve Your Carrier, Bank, and App Support
Carriers can help secure your SIM, reset roaming patterns, and block unauthorized activations. Banks and payment providers should be alerted to potential fraud, and you may need to issue temporary security holds or issue new cards. App developers and support channels can assist with revoking sessions, resetting credentials, and preventing future unauthorized access. Document the timeline of events, including when you noticed anomalies and which steps you took, to speed up investigations and dispute processes.
Long-Term Prevention: Password Hygiene and Security Habits
After restoring control, shift to strong, sustainable security habits. Use a password manager to generate unique, long passwords for every account and enable MFA on all services. Regularly review app permissions, enable automatic OS updates, and avoid sideloading apps from untrusted sources. Consider a security audit at periodic intervals and stay vigilant for phishing attempts or suspicious behavior. Establish routine checks for account activity and device health, so you’re prepared if another breach occurs.
Tools & Materials
- Smartphone with the latest OS(Ensure it is fully charged and accessible; pending updates should be installed.)
- Password manager app(Choose a reputable manager; enable auto-fill only on trusted devices.)
- Two-factor authentication (2FA) enabled across accounts(Use an authenticator app when possible; avoid SMS-based codes.)
- Secure backup solution(Back up contacts, messages, photos, and app data to a trusted location.)
- Malware scanning tool(Install from official app stores; perform a full device scan.)
- Trusted recovery emails and backup codes(Verify access to recovery options before incident response.)
- A trusted computer or another device(Used to review accounts and reconfigure security settings safely.)
Steps
Estimated time: 2-4 hours
- 1
Pause usage and secure network
Power off or disconnect from all networks if you suspect remote access. This halts further data transfer and buys time to assess the breach.
Tip: If you can, enable airplane mode to stop all network activity temporarily. - 2
Change critical passwords from a trusted device
Log into key accounts (email, banking, cloud) from a secure device and create unique, strong passwords.
Tip: Use a password manager to generate and store complex passwords. - 3
Enable and verify 2FA on essential services
Turn on two-factor authentication and verify all accounts support authenticator apps over SMS where possible.
Tip: Keep backup codes in a secure location separate from the device. - 4
Review and revoke suspicious permissions
Check installed apps for unusual permissions and remove anything unfamiliar.
Tip: Disable background activity for apps you don’t trust. - 5
Run a malware scan and update software
Install a trusted security app and perform a full device scan; apply OS and app updates.
Tip: Do not ignore prompts for critical security patches. - 6
Back up data before major changes
Create a clean backup to a trusted cloud or local device before any reset.
Tip: Verify backup integrity by testing a small restore. - 7
Consider a factory reset if issues persist
If the device remains compromised, reset to factory settings after backing up important data.
Tip: Only reinstall apps from official stores; avoid sideloading. - 8
Restore data and re-secure
Restore essential data selectively and reconfigure security settings with MFA enabled.
Tip: Set up device protection like a PIN/biometrics and screen lock. - 9
Monitor and document activity
Track account activity and keep a log of steps taken for investigations and future prevention.
Tip: Set up alerts for unusual login attempts.
Got Questions?
What should I do first if I think my phone is hacked?
Identify suspicious activity, disconnect from networks if possible, change critical passwords from a trusted device, and run a malware scan. Then assess whether a factory reset is needed.
Start by identifying suspicious activity, disconnect from networks, change key passwords from a trusted device, and scan for malware. If symptoms persist, consider a factory reset.
Can I recover data after a factory reset?
Yes, if you have a recent backup stored securely. Restore from backup after the reset and reinstall apps only from official sources.
Yes, you can recover data if you have a backup. Restore the backup after resetting and reinstall apps from official stores only.
Should I reuse passwords after a hack?
No. Reusing passwords keeps you vulnerable. Create unique passwords for every service and enable MFA.
Definitely not. Use unique passwords for each service and enable MFA to reduce risk.
Is it important to contact my carrier?
Yes. Your carrier can resecure your SIM, investigate anomalies, and block unauthorized activations.
Yes. Contact your carrier to resecure your SIM and block unauthorized activations.
How can I tell if a malware is on my phone?
Common signs include unusual battery drain, pop-ups, overheating, and unfamiliar apps. Run a security scan if you notice any of these.
Look for battery drain, strange pop-ups, and unfamiliar apps. Run a trusted security scan if you notice them.
Do iPhone and Android differ in response to hacks?
Both require password hygiene, MFA, and updates, but the exact steps may differ between OS ecosystems and app stores.
Both platforms require MFA and updates; specifics vary a bit between iOS and Android.
Watch Video
What to Remember
- Act quickly to limit damage and preserve evidence.
- Secure accounts with MFA and unique passwords.
- Back up data before making major changes.
- Update OS and apps, then re-secure the device.
- Monitor accounts for unusual activity and stay vigilant.