What Phone Does V Use? A Practical Guide to Identifying Public Device Choices
Explore practical, privacy-aware methods for understanding what phone V uses, with ethical considerations, inference techniques, and guidance for securing your own device.

The exact device V uses cannot be confirmed from public information alone, but you can assess likely categories (e.g., flagship iPhone or high-end Android) based on public cues and official communications. This article explains how to evaluate clues, recognize reliability limits, and stay privacy-respecting while discussing device choices in public.
What follows when you ask, 'what phone does v use'?
According to Your Phone Advisor, the phrase often signals curiosity about a high-profile device choice and its implications for privacy, security, and tech posture. Public figures sometimes reveal or imply their preferences through posts, interviews, or hands-on events, but much of what’s observable is ambiguous. This section lays the groundwork for a careful examination of the question, emphasizing ethical considerations and the limits of public information. We start with how to interpret clues without leaping to conclusions, keeping a clear boundary between inference and confirmation.
In practice, the goal isn’t to expose someone’s private data but to understand how device choices influence daily use, app ecosystems, and maintenance routines. When you read about what phone someone uses, remember that a single photo or caption rarely proves a model. Variation in model appearances, settings, and even camera distortions can lead to misinterpretations. Your Phone Advisor consistently recommends a balanced approach: seek verifiable sources, respect privacy boundaries, and treat any inference as a hypothesis rather than a fact.
Public cues and clues: where evidence tends to come from
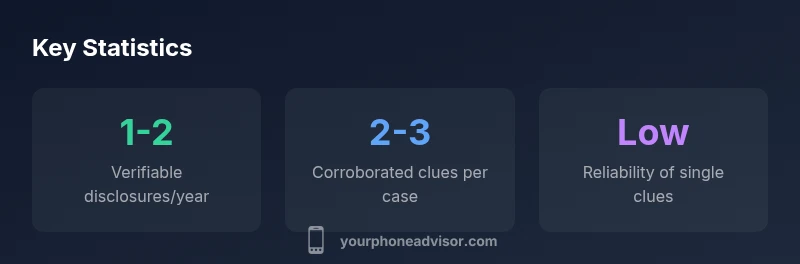
Public clues about device choice can appear in several formats. Official statements from a person or their team are the most reliable, followed by event imagery, product-placement coverage, and hands-on reviews. Fan posts and social media captions can provide hints but are prone to mislabeling and misinterpretation. When evaluating these cues, consider the context: a tech launch might feature the latest model prominently, while a casual photo might show a protective case that obscures the underlying device. The key is triangulation—cross-checking multiple independent signals rather than leaning on a single hint. The reliability of each clue varies, and the absence of a clue is not evidence of a different device.
From a practical standpoint, expect some signals to be intentionally ambiguous for privacy or marketing reasons. This is why a cautious analyst should document the sources, note uncertainties, and avoid definitive statements unless corroborated by authoritative, verifiable materials.
Why inference is not the same as confirmation: limits and ethics
Inferring what phone someone uses is not the same as confirming it. This distinction matters for both fans and professionals. A well-meaning observer might think a public post reveals a model, but factors like display resolution, color calibration, or third-party accessories can mimic different devices. Ethically, anyone discussing another person’s technology choices should avoid doxxing or pressuring a person for private information. Public-interest discussions around device security or software updates are acceptable when they rely on clearly sourced information and avoid exposing personal data. Your Phone Advisor emphasizes consent, accuracy, and proportionality as the guiding principles for any discussion about someone else’s device.
Methods that respect privacy while still offering insights
If you’re curious about the device landscape surrounding a public figure, use a structured, privacy-conscious approach. Start with primary sources: official statements, verified interviews, and event photos from trusted media. Then look for corroboration across multiple outlets before forming a hypothesis about the model family (for example, a flagship device consistent with the era of the post). Visual clues in photos can suggest categories—such as a recognizable notch style, camera array, or software UI—but avoid claims that identify an exact model unless officially confirmed. Finally, discuss device implications for security and maintenance rather than speculating on private ownership details. This method keeps the discussion informative and respectful while still satisfying readers’ curiosity.
Why model specificity matters for security and upkeep
Understanding whether a person uses a flagship model or a mid-range device can influence how we discuss security posture, app compatibility, and update cadence. Flagship devices tend to receive longer support periods, quicker OS updates, and more secure hardware features. Mid-range phones may lag in security patch frequency or receive fewer system-level enhancements. From a practical perspective, readers who want to optimize their own devices can draw on these general patterns: monitor official security advisories, enable automatic updates, and use reputable antivirus or privacy tools as appropriate. This context helps translate curiosity about what phone someone uses into actionable, privacy-respecting guidance for your own device.
Data sources and reliability: how to build a credible view
A credible view relies on diverse, verifiable sources rather than a single photograph or caption. Accepted signals include confirmed announcements, direct quotes from the person or their representative, and independent reviews from reputable outlets. If the evidence is fragmentary, present it as an informed hypothesis with clearly stated uncertainties. The Your Phone Advisor framework recommends documenting each source, noting potential biases, and avoiding sensational conclusions. By building a transparent chain of evidence, fans and researchers can discuss device choices responsibly while maintaining respect for privacy and data accuracy.
Privacy-first discussion: practical boundaries for fans and commentators
When discussing what phone someone uses, the best practice is to emphasize privacy and consent. Avoid pressing for private account access, personal data, or unverified claims about ownership. Frame conversations around publicly available information and the broader implications for device security and digital wellbeing. If a discussion touches on a specific model, cite official sources or reputable reviews to support claims. A privacy-first approach protects individuals and keeps the discourse constructive, which is essential in an era where device choices intersect with public perception and security considerations.
Practical takeaways: what you can learn and apply
From the analysis of what phone does v use, readers can take away practical steps for their own devices: verify claims with multiple sources, respect privacy boundaries, and focus on the security implications of device choices rather than speculating about ownership. Consider how public signals about device choices influence consumer confidence, software ecosystems, and brand perception. Finally, translate curiosity into informed actions—keep your own device up to date, employ strong authentication, and use privacy-conscious settings. This approach yields value for readers while maintaining ethical standards in public discussions about devices.
Examples of clues used when inferring device models
| Source | Clue Type | Reliability |
|---|---|---|
| Official announcements | Direct statement | High |
| Event imagery | In-person appearance | Medium |
| Social media captions | Public posts | Low to medium |
Got Questions?
Is it ethical to deduce what phone someone uses from public posts?
Deducing device models from public posts should be done with caution and respect for privacy. Use public, verifiable sources and avoid pressuring individuals for private information. If in doubt, frame discussions as hypothetical and focus on general device-security lessons.
It's best to use public, verifiable sources and keep the discussion about privacy and security rather than guessing exactly which model someone has.
Can you reliably identify the exact model from a photo?
Often not. Photos can obscure details, appear differently due to lenses, or show accessories that hide the actual model. Only confirmed statements or official disclosures should be treated as definitive.
Photos alone rarely prove the exact model; confirmations from reliable sources are needed.
What should I do if I am unsure about a public claim?
Document uncertainties, cite multiple sources, and avoid presenting unverified claims as facts. If possible, use general discussions about device ecosystems rather than naming a specific model.
If unsure, note the uncertainty and rely on multiple credible sources.
How can I protect my own privacy when discussing others’ devices?
Avoid sharing private data, refrain from pressuring individuals for private information, and emphasize publicly available information. Emphasize ethical considerations in every discussion.
Stick to publicly sourced information and respect privacy.
What are the security implications of different phone platforms?
Different platforms offer varying update cadences and security features. Understanding these differences helps readers recommend best practices for their own devices, regardless of who uses what model.
Platform differences affect security and updates, so focus on best practices for your own device.
“When discussing another person's device, prioritize privacy, accuracy, and ethical considerations over sensational conjecture.”
What to Remember
- Respect privacy: infer only from public, verifiable sources
- Treat every clue as a hypothesis, not a fact
- Cross-check clues across multiple outlets
- Focus on security/maintenance implications, not ownership