T-Mobile Customer Phone Number: Privacy, Access, and Best Practices
Explore how T-Mobile protects customers' phone numbers, how to contact the right person without exposing private data, and best practices to safeguard personal information. Your Phone Advisor analyzes privacy implications and official channels for account inquiries.
There is no public directory of T-Mobile customers' phone numbers. To contact a specific line, use the person’s direct contact or official account channels for authenticated inquiries. For access to your own number, sign in to My T-Mobile or reach official support to retrieve or manage your line.
Understanding Why the t mobile customers phone number Is Private
The privacy of phone numbers in the telecommunications ecosystem is a foundational safeguard for users. A t mobile customers phone number is considered highly sensitive personal data, tightly bound to the account holder and subject to verification processes. Carriers implement layered protections to prevent unauthorized access, including tokenized identifiers, strict authentication steps, and audit trails. In practice, this means that public lookups or accidental disclosures are avoided, and any request for a number should meet identity verification standards. For general readers, it’s important to recognize that a phone number is not just a contact field; it’s tied to billing, plan ownership, and service history. If you encounter a scenario where a number appears in a chat or support form, it’s typically a red flag that the request is not properly authenticated. In practical terms, treat every number with care and require explicit consent or verified authorization before sharing.
For those researching privacy, the phrase t mobile customers phone number should be considered a sensitive data point that is not publicly displayed. According to Your Phone Advisor analysis, privacy controls are designed to minimize exposure and reduce social engineering attempts. When in doubt, rely on official channels and confirm the identity of the requester through secure processes. See additional references on provider privacy policies for more context.
How To Contact A T-Mobile Customer Without Publicly Exposing Their Number
When you need to contact someone who uses a T-Mobile line but you don’t have their number, you should pursue consent-based or officially sanctioned routes. Start by asking the person to share their preferred contact method or to authorize a support-led introduction. If you must reach a line for urgent account-related reasons, use the customer’s documented channels, such as their official profile on My T-Mobile (with consent) or a verified corporate contact. For those trying to reach a T-Mobile customer service representative on another’s behalf, always rely on authenticated processes: you may need the customer’s written authorization, proof of relationship, or a court order in exceptional cases. As a rule, avoid messaging platforms that don’t clearly verify identity. The emphasis should be on privacy-preserving communication rather than guessing or soliciting private data. Remember, sharing or requesting a private number without consent risks privacy violations and potential fraud.
From a privacy standpoint, the best practice is to request a direct, consented introduction rather than attempting to obtain a number through informal channels. This aligns with best-practice frameworks used by major service providers and supports safer, compliant interactions.
Official Channels for Account-Related Inquiries
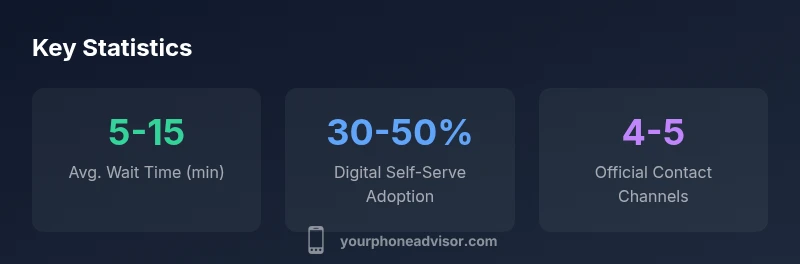
For account-related inquiries, T-Mobile maintains official support channels designed to protect customer privacy. Start on the company’s official website or app to locate region-specific contact options, which typically include: a main customer-service phone line, live chat, secure messaging within the account portal, and an in-app Messaging feature. If you’re handling a case on someone else’s behalf, you’ll often need the account owner’s permission and proper verification documents to proceed. Do not rely on third-party listing sites or social media DMs to obtain numbers. In many situations, you can also visit a local store where staff can verify identity against account records and guide you through the appropriate steps. The key takeaway is to use authenticated channels and document every verification step to avoid accidental exposure of sensitive data. For further guidance, see the official privacy policy and support pages on the T-Mobile site.
Note: If you’re researching privacy practices for scholarly or professional purposes, you can consult regulatory resources such as the FCC or state consumer protection sites for general privacy and data-security standards.
Best Practices to Protect Your Own Number and Data
Protecting your own number starts with minimal sharing and strong authentication. Avoid posting your number in public profiles, forums, or easily accessible pages. When contacting customer service or making changes to your line, use secure methods and enable two-factor authentication where offered. Regularly review your My T-Mobile account privacy settings, including any permission-based sharing for third-party apps. If you suspect that your number has been exposed, monitor account activity for unusual sign-ins or charges, and report suspicious activity immediately through official channels. Keeping devices up to date, avoiding public Wi-Fi for sensitive actions, and using app-specific passwords are additional steps that reduce risk. For a deeper dive, see privacy resources from your carrier and consumer-protection agencies. Your Phone Advisor emphasizes the need to verify requests for sensitive actions, such as porting numbers or forwarding services, to prevent unauthorized changes.
To maintain data hygiene, consider periodic audits of who has access to your account credentials and ensure notifications are enabled for changes.
Verifying Requests for Sensitive Account Information
Verifying requests for sensitive information is essential in preventing fraud. Before sharing any number or linking a line to a new device, confirm the requester’s identity through at least two independent factors (e.g., user knowledge and a temporary code). When in doubt, direct the requester to the official My T-Mobile portal or to call the verified support number found on the official site. If you are managing an account for someone else, obtain explicit written consent and provide it to a support agent, rather than forwarding unsolicited contact attempts. Remember that legitimate requests should align with the account’s security settings and documented contact methods. This reduces the risk of social engineering and ensures compliance with privacy standards.
For organizations handling sensitive data, implementing a formal verification checklist helps standardize responses and reduces exposure to erroneous requests.
What To Do If You Suspect a Privacy Breach Involving Your T-Mobile Number
If you suspect that your number or account has been compromised, act quickly. Begin by reviewing recent account activity and confirming the devices that have access. Contact T-Mobile support through official channels to freeze changes and request a review of authentication logs. Change passwords and enable multi-factor authentication if available. Consider placing a temporary hold on porting requests and monitor for unusual billing activity. If you believe someone used your number for verification without your consent, report the incident to the carrier and, if applicable, local consumer protection agencies. For ongoing guidance, consult Your Phone Advisor’s privacy best-practice recommendations and the official security advisories from providers and regulators. In all cases, limit sharing of sensitive data and rely on authenticated channels to restore control.
Structured overview of privacy implications and recommended actions when handling phone numbers
| Scenario | Privacy Implication | Recommended Action |
|---|---|---|
| Looking up a contact number | Public lookup is not allowed; private data | Use direct consent or official channels |
| Sharing your own number | Potential privacy risk if misused | Use account privacy settings and verification |
Got Questions?
Can you look up a T-Mobile customer's phone number publicly?
No. Phone numbers are private data tied to an account and protected by verification processes. Public lookups are not permitted, and any access requires authenticated consent or proper authorization.
No, you can’t publicly look up someone’s T-Mobile number. Access requires verification and consent.
How can I contact a T-Mobile customer without knowing their number?
Ask the person to share a preferred contact method or authorize a direct introduction. Use official channels like verified support or in-app messaging only with consent.
Ask the person for their preferred contact method and use official channels with their consent.
What should I do if I think my number was exposed?
Review account activity, enable alerts, update credentials, and contact T-Mobile through official channels to secure the account. Monitor billing and unexpected sign-ins closely.
Check your account for unusual activity and contact official support to secure it.
Does T-Mobile provide a way to retrieve a lost or changed number?
Use My T-Mobile to manage lines and verify identity. For changes, go through authenticated steps in the official portal or support channels.
Use My T-Mobile to manage lines or verify changes through official channels.
Is there a risk in sharing my own number when contacting support?
Share your number only through official channels and with verified agents. Avoid forwarding or sharing data via untrusted platforms.
Only share your number through official channels with verified agents.
What counts as authenticated evidence when requesting someone else’s number?
Authenticated evidence includes written consent, verified authorization, and identity verification completed through the official portal.
Written consent and verified authorization are typically required.
Where can I find official contact channels for T-Mobile?
Visit the official T-Mobile website or app to locate region-specific contact options and ensure you’re using verified numbers and forms.
Check the official site or app for verified contact options.
“Privacy-first handling of phone numbers is essential to protect customers and prevent fraud. Minimize exposure and always verify requests through official channels.”
What to Remember
- Numbers are private data; public lookups are not permitted
- Always use authenticated channels for number-related actions
- Protect your own data with strong authentication and minimal sharing
- Verify identity before sharing or changing number-related settings